NOTE TO CREEPS: DIGITAL STALKING IS STALKING
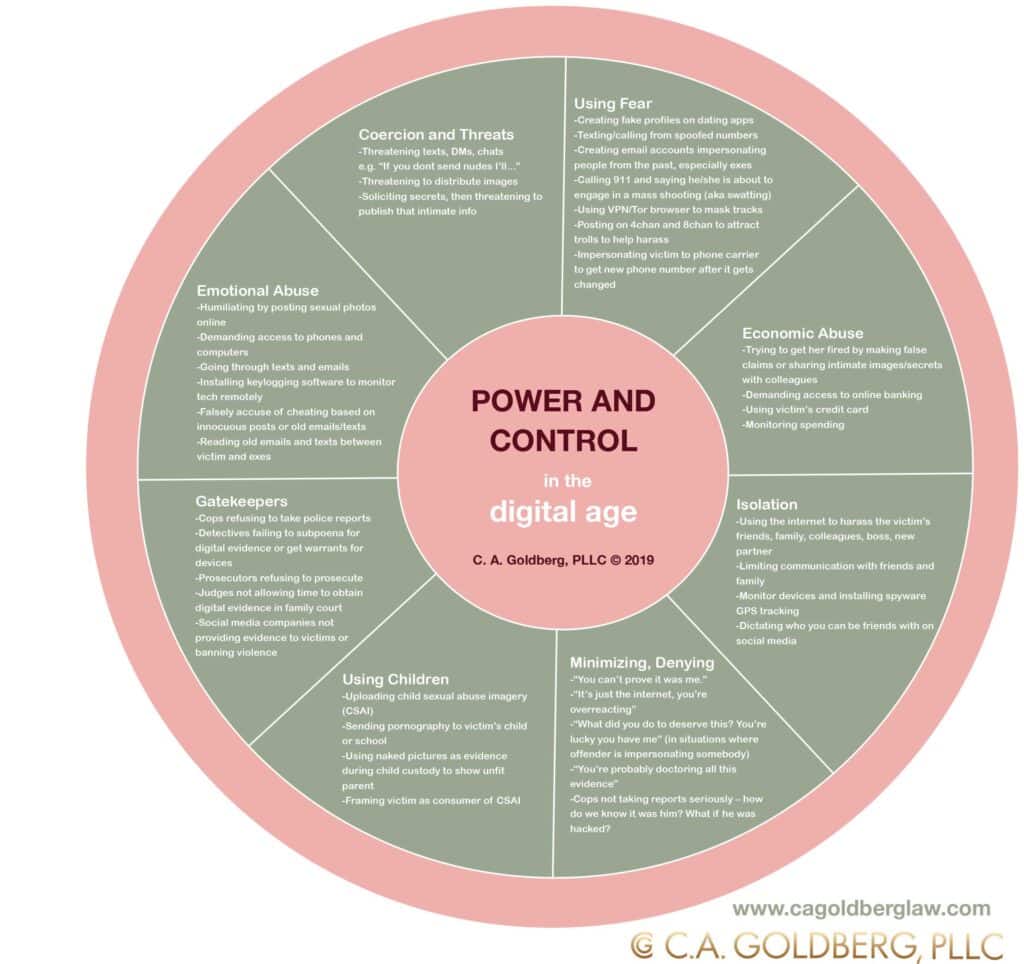
It’s 2019 and, as technology has progressed, so have the psychos and abusers stalking us on and offline. One of the ways an asshole partner or creepy hacker can monitor you or steal your information is through keylogging software.
What is keylogging software?
Keyloggers are programs that can be downloaded onto your computer or phone to secretly watch what you’re doing online. They work by recording every move you make when you’re typing and navigating your device.
Offenders can use keyloggers to do things like snatch your passwords, record the websites you’re visiting or what you’re searching on Google, or capture what you’re writing in a (supposedly) private email or text. Most keylogging software can also take screenshots of your device.
All of this information can be stored either on your hard drive or in the cloud. The software can also send reports containing all your personal data to a remote location where the offender can access it.
Keylogging programs are often used to steal usernames and passwords, banking information, or secrets that can be used to control or extract money from a victim.
All of this can happen without you having the slightest clue.
How did this get on my computer in the first place?
Many of these programs bill themselves as being useful for parents to ‘monitor’ their kids and are widely available on the app store. Keylogging software can easily be downloaded from the internet and hidden on your device, if you leave your laptop open while you go to the bathroom, for example.
Keylogging software can also be installed on your device is through ‘malware packages’. Malware (short for “malicious software”) is any program that is harmful to your computer, such as a virus. If you accidentally follow a sketchy email link, download a program from the internet, or click on the wrong ad, you could download a keylogger without even realizing. Once it’s on your device, these sneaky bugs will conceal themselves by being installed in hidden folders,
or hiding the application from the operating system task list, such as the Windows task manager or the Mac activity monitor. Hackers use the keyloggers installed by malware packages to steal credit card information, access personal data that they can use to extort you, and just about any other creative form of abuse they can think of…
How do I know if my device is infected and what can I do to get rid of the software?
There are a bunch of different ways to figure out if there’s a keylogger lurking on your device, but none of them are guaranteed to find it. That’s why you should always try a variety of different methods to be safe. The first thing to do is to run an antivirus program on your system, which can usually detect keylogging software. There are also other, more specialized programs you could download, including Spybot Search & Destroy and Malwarebytes, which will check for certain types of malware.
Another thing you can do is check which programs are currently running on your computer. On a Mac, look on your Activity Monitor. If you’re using Windows, press ctrl+alt+del. Look at the “tasks” currently running on your computer. If you don’t recognize any of them, or they look suspicious, plug the name into a search engine and see what comes up.
If you find a keylogger on your device, check to see if there is an option to uninstall it like other programs. Sometimes downloading the installer for the keylogger will also let you uninstall it. If you can do that, run your anti-malware program afterwards to remove any traces. There are some specific anti-logger programs you can download too, and those will be your best bet for detecting new keyloggers and helping you get them the f*ck off your device. Even if you think it’s gone, it may not be – so please use caution.
When should I start to suspect that my partner has installed a keylogger?
If your partner is already behaving abusively in other ways, such as closely monitoring your social media posts, dictating with whom you can communicate online, or demanding access to your phone, then it’s possible he may also be monitoring your online activity using a keylogger.
He might also slip up and reveal that he knows things he shouldn’t, like something you mentioned to a friend via text or recently searched on Google. Or maybe you get an email about a new login to your Facebook or bank account. Even if it’s just a gut feeling, you should trust your instincts and check to see if you’re being monitored. Start using an Incident Tracking chart, if appropriate, to keep a record of evidence which could be used later on.
If your partner or ex is cyberstalking you, we’re here to help. We can help you figure out a plan to stay safe, such as getting an Order of Protection. Using technology like keyloggers to monitor your online behavior is how these psychos try to control you. We’ll help you take back your personal life, take back your privacy, and take back your power.
Is keylogging illegal?
YES. Secretly installing a keylogger is a serious violation of law. Viewing the results of that spying is illegal too, and if the psycho uses any of the information illicitly gained through the use of a keylogger, even more charges can be brought. Stalkers: you’ve been warned.
A note on pronouns: We tend to use female pronouns when talking about victims of abuse, and masculine pronouns when talking about perpetrators. This is a deliberate choice based on a number of things, including the demographics of our clients. It is essential to note that men can be victims of abuse and women can be perpetrators of it. Abuse happens both in straight and same-sex relationships. Two in five gay or bisexual men will experience intimate-partner violence in their lifetimes. Half of all lesbian women will experience it. Transgender people are at the highest risk of intimate partner violence and are 2.6 times more likely to experience it than a straight person.




